Splunk
This guide provides instructions on how to activate the Splunk connector within VirusTotal. Once activated, VirusTotal reports will display threat intelligence information about IoCs (Indicators of Compromise) sourced from the events found in your Splunk instance.
Prerequisites
Before you can begin the connector set up, ensure that you have the following prerequisites in place:
-
Access to Splunk: You must have access to a instance of Splunk, either Enterprise or Cloud.
-
Access token: Obtain a access token from your Splunk instance. This token will be required for authentication during the integration setup.
Getting the Splunk access token
Follow these steps to get the Splunk access token:
-
Access to the Splunk instance
-
Navigate to the Tokens page: Open
Settingstop menu and click onTokensunderUSERS AND AUTHENTICATIONsection. -
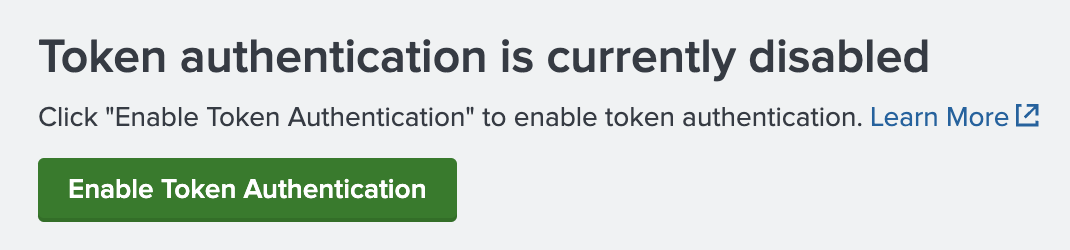
Enable Token Authentication: Token authentication is disabled by default, enable it cliking on the button.
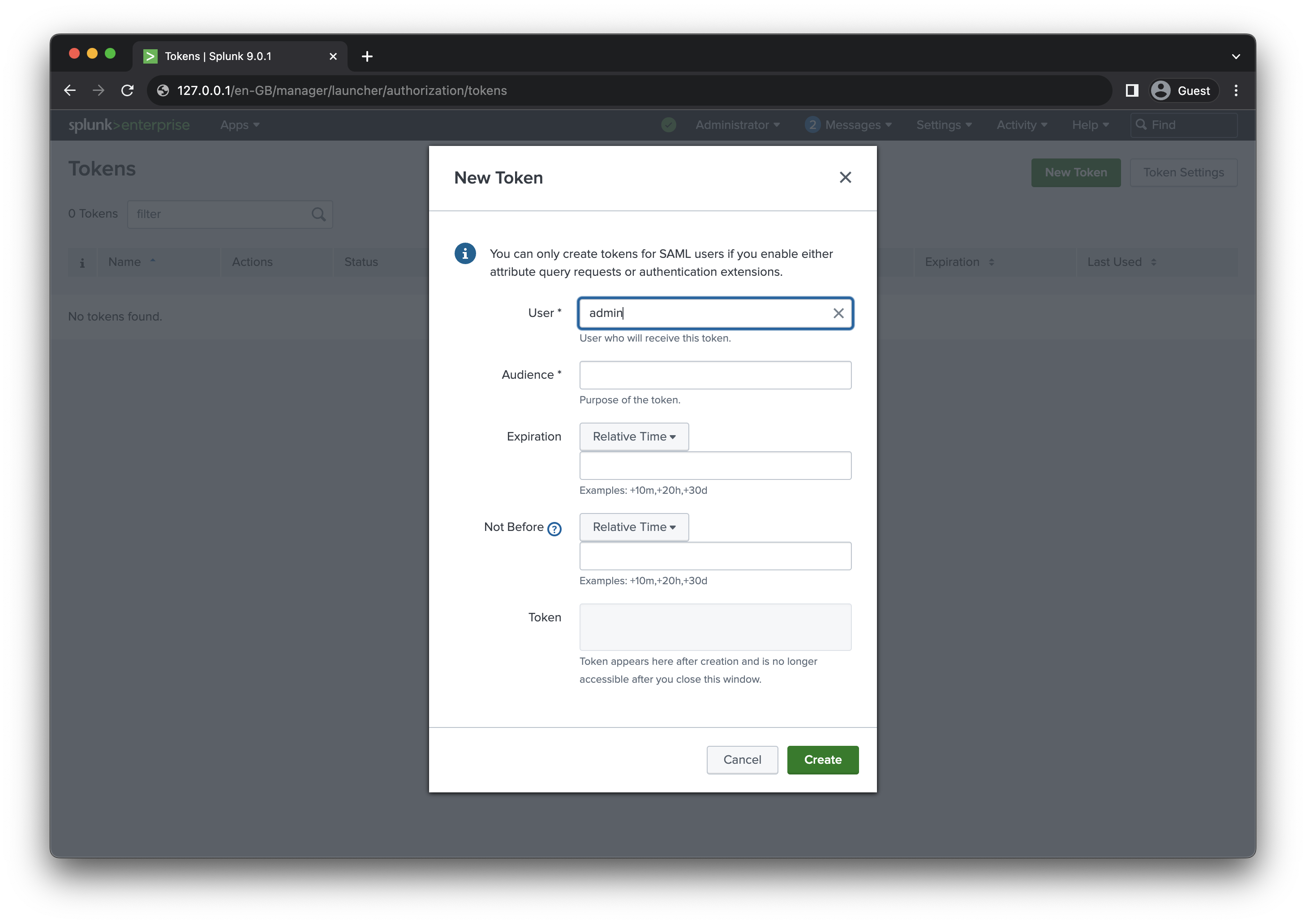
- Create a new token: Click on
New Tokenand fill the `Audience`` field, create and copy the token.
Adding the connector
Before you can view Splunk events information in VirusTotal reports, you must set up the Splunk connector and provide your access token. Follow these steps:
- Access the
Technology Integrationspage via the left menu and then click on theConnectors (Third party to VT). This page serves as the hub for all your configured connectors.
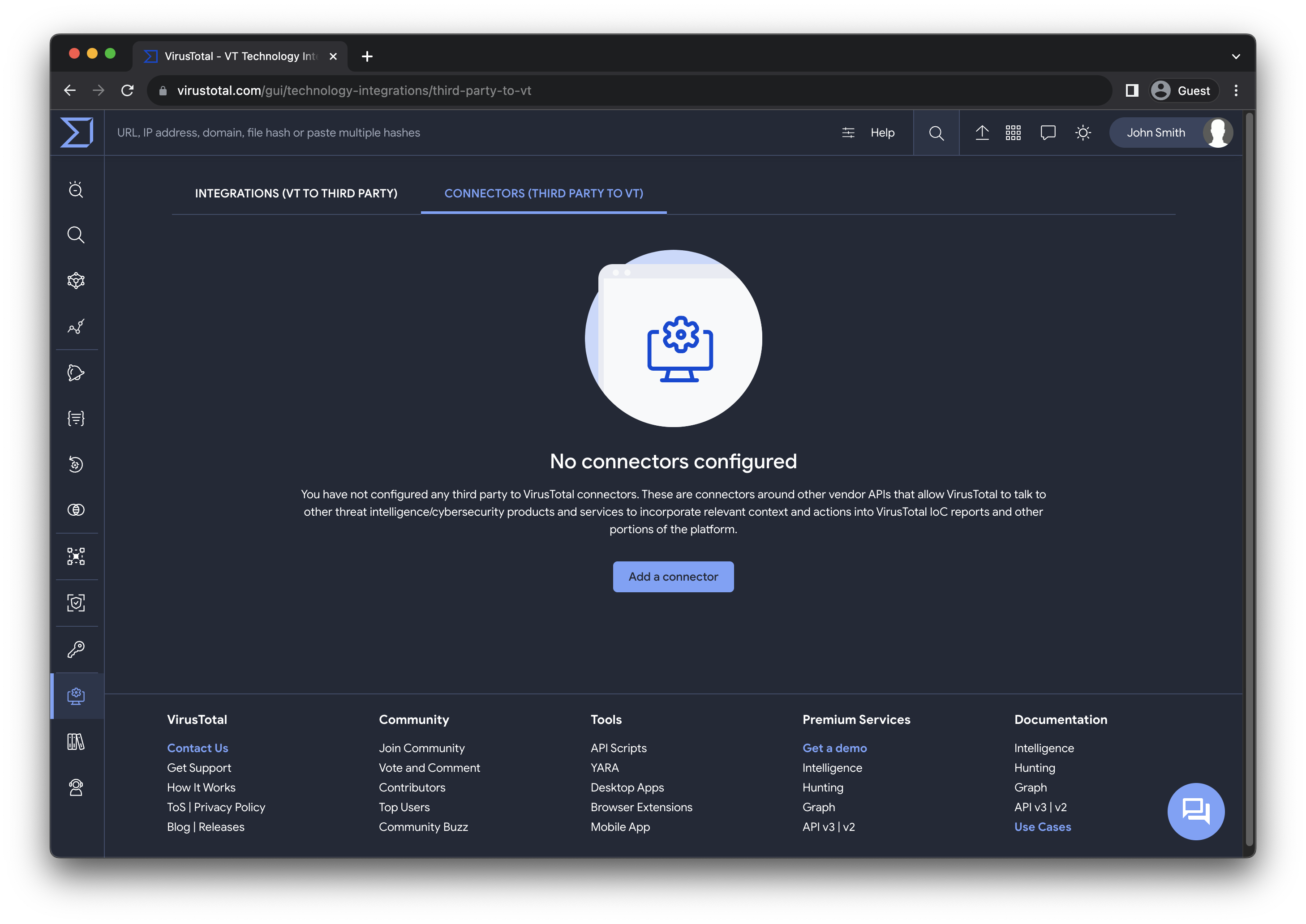
Here you can perform different actions described in details in the Manage the connector section.
-
Click on
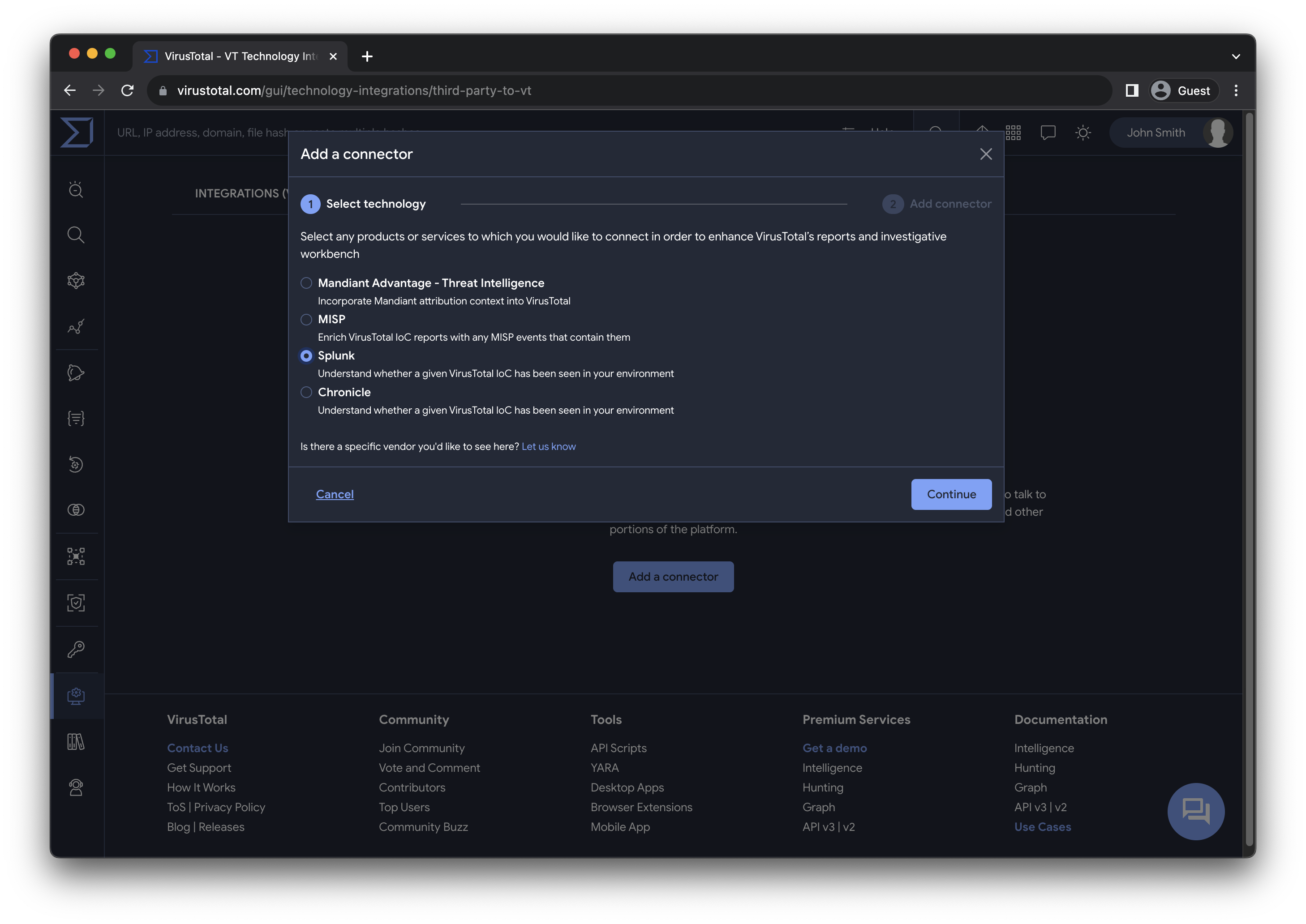
Add a connector. A dialog will guide you through configuring the connector in two straightforward steps. -
Select the Splunk connector.
- Provide a name, the access token, a list of Splunk sourcetypes to filter the events and the URL of your instance.
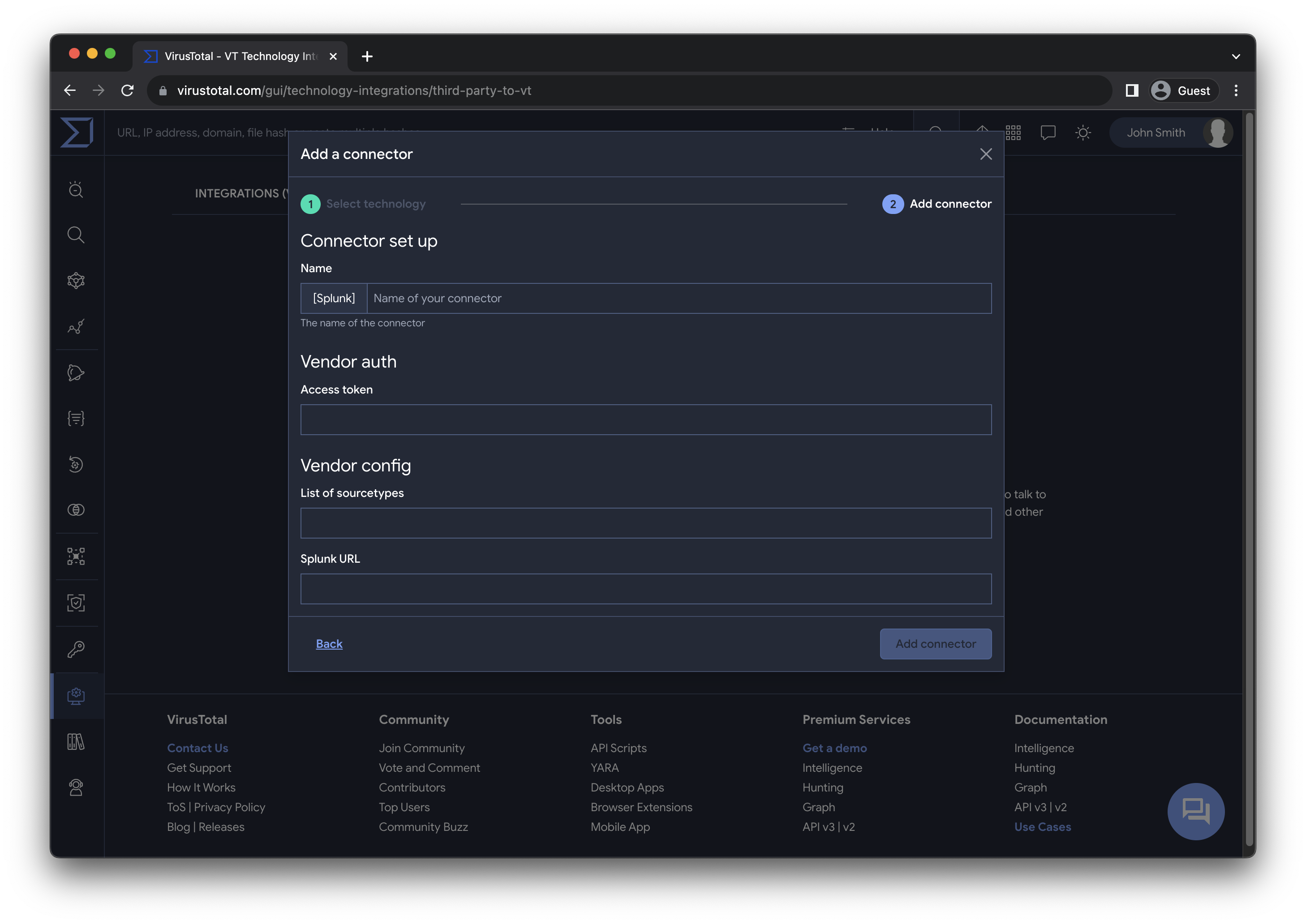
- Save the connector.
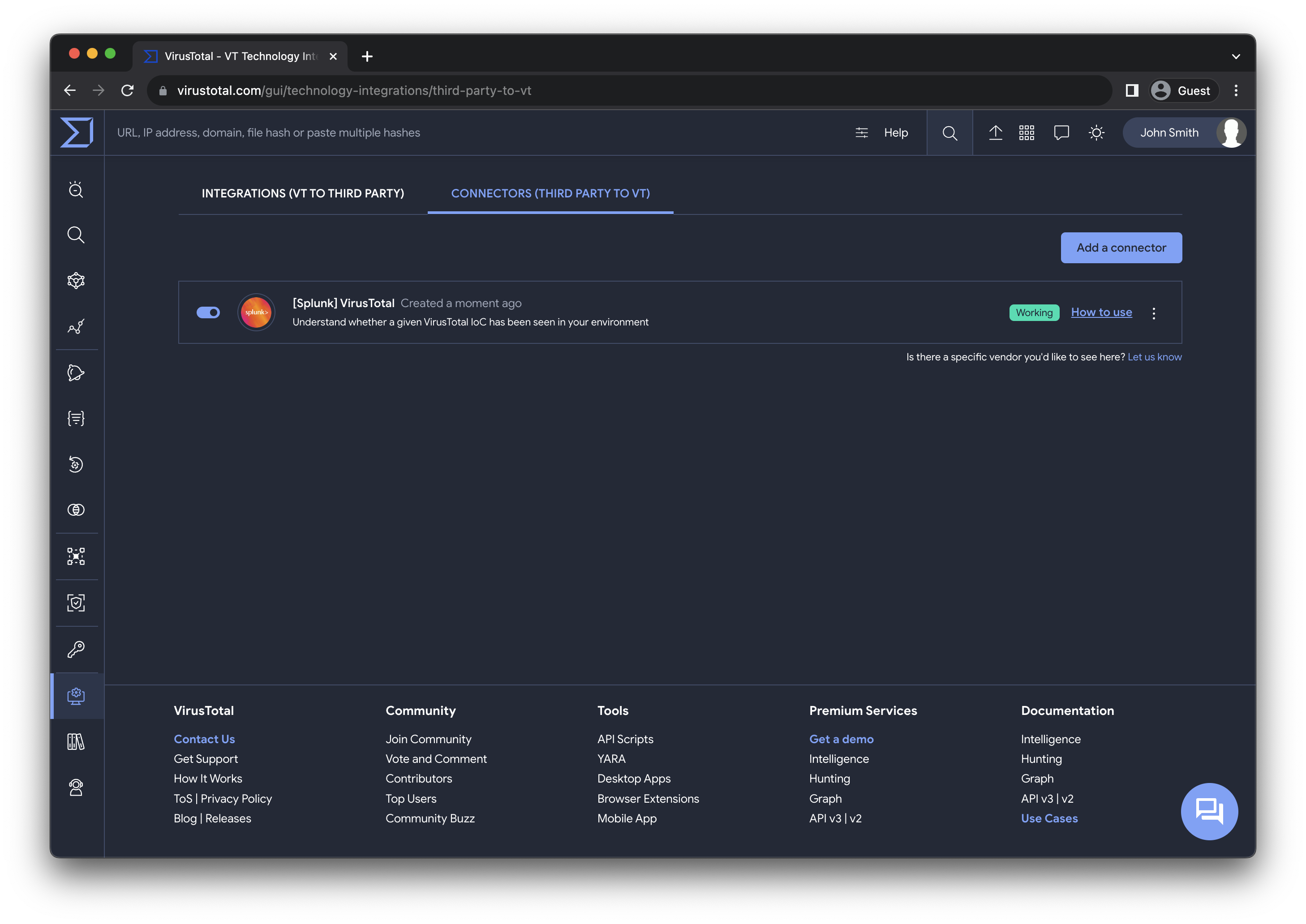
Once completed, all members of your group will have access to the Splunk events information in the IoC reports.
Managing the connector
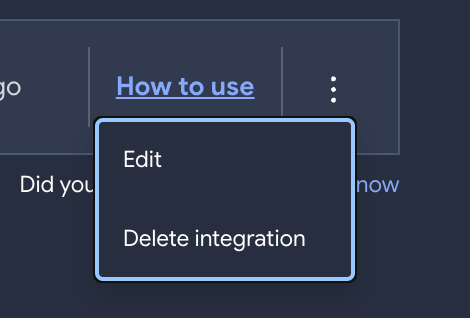
The user who adds the connector and the admins of the group to which it belongs, has the authority to edit or delete the connector.
Additionally, all users within your group can enable or disable the connector, this action affects individually to the user.
Viewing Splunk Information
Once the Splunk connector is configured, all members of your group will start seeing additional context in the reports.
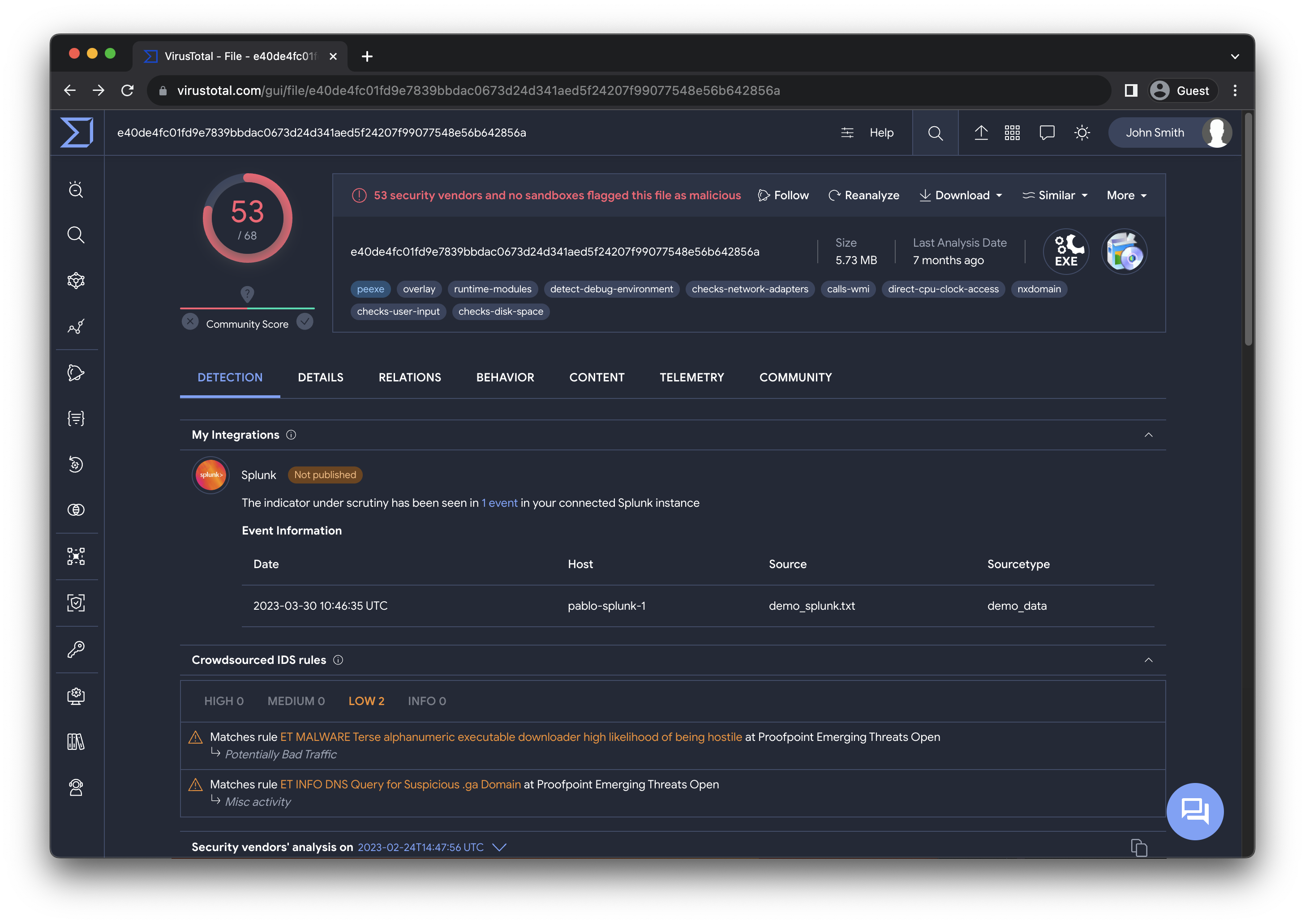
For each IoC, you will receive some information related to the Splunk event, the date host, source and sourcetype.
Support
This connector is officially suported by VirusTotal, please contact us if you have any question.
Updated 6 months ago
